The cybersecurity landscape of 2025 has been marked by unprecedented data breaches that have exposed billions of records, cost organizations millions of dollars, and fundamentally changed how businesses approach digital security. While the global average cost of data breaches decreased to $4.44 million in 2025: representing a 9% drop from 2024's record highs: this statistic masks a more complex reality. United States organizations faced their highest breach costs ever, with expenses surging 9% to reach $10.22 million per incident.
These figures represent more than statistical data points; they reflect real businesses facing operational disruption, regulatory penalties, and long-term reputational damage. Understanding the major breaches of 2025 and their financial implications provides crucial insights for business leaders seeking to protect their organizations from similar threats.
The Year's Most Devastating Breaches
Mars Hydro: The Largest Breach by Volume
February 2025 witnessed what may be the largest data exposure in terms of sheer volume when Mars Hydro, an Internet of Things device manufacturer, suffered a breach exposing 2.7 billion records. This incident highlighted critical vulnerabilities in IoT infrastructure that many businesses overlook. The exposed data included Wi-Fi passwords, IP addresses, email addresses, and device configuration information: creating a cascading security risk for millions of users whose connected devices suddenly became vulnerable entry points for cybercriminals.
The financial cost to Mars Hydro remains undisclosed, but industry experts estimate remediation efforts, legal fees, and regulatory compliance costs likely exceeded $50 million, not including the immeasurable damage to consumer trust in IoT security.

Google and Apple Credential Exposure: Tech Giants Vulnerable
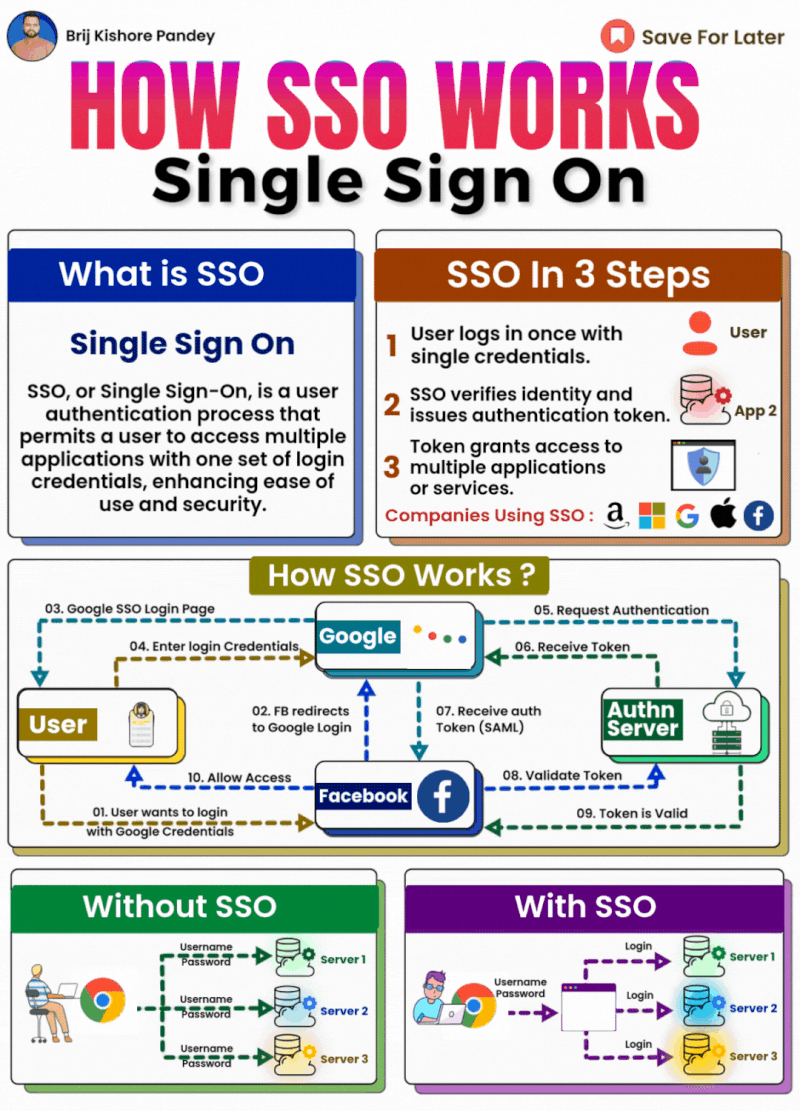
May 2025 delivered a shocking revelation when cybersecurity researcher Jeremiah Fowler discovered an unprotected database containing 184,162,718 unique login credentials for major platforms including Google, Apple, Microsoft, Facebook, Instagram, and Snapchat. The database sat online without password protection, making these credentials freely accessible to anyone who discovered the server location.
Investigation revealed the data originated from infostealer malware that harvested credentials from infected devices over an extended period. While neither Google nor Apple directly caused this breach, the incident demonstrated how third-party compromises can expose even the most security-conscious organizations. The affected companies faced significant costs in forced password resets, user notifications, and enhanced security measures, though specific financial figures were not disclosed.
Coinbase: When Insider Threats Turn Costly
The cryptocurrency exchange Coinbase experienced a particularly damaging breach in May 2025 when overseas customer support contractors leaked sensitive information belonging to 69,461 users. The exposed data included full names, contact information, partial Social Security numbers, and identification document images. While no cryptocurrency funds or cryptographic keys were compromised, cybercriminals attempted to extort $20 million from the company.
Industry analysts estimated Coinbase's total breach-related costs at approximately $400 million when accounting for incident response, regulatory fines, legal settlements, and customer compensation programs. This incident particularly highlighted the risks associated with third-party contractors and offshore support operations.
TeleMessage: Government Communications Compromised
Perhaps the most politically sensitive breach of 2025 occurred when hackers gained access to TeleMessage's servers, which hosted a modified version of the Signal messaging app used by US government agencies for secure communications archiving. Within just 20 minutes of gaining access to the AWS-hosted server, attackers extracted names, message fragments, and contact information of government personnel using .gov email addresses.
While the full financial impact remains classified, sources within the federal government suggest remediation costs exceeded $100 million when including emergency security upgrades, personnel reassignments, and enhanced vetting procedures for government communication platforms.
Understanding the Financial Impact
The cost structure of data breaches in 2025 revealed several concerning trends that every business leader should understand. Cloud-based incidents proved particularly expensive, with 72% of all breaches involving cloud-stored data and multi-environment incidents averaging $5.05 million in costs.
Third-party vendor compromises emerged as both the second most common attack vector and second costliest breach type, with average expenses reaching $4.91 million per incident. This trend was exemplified by numerous retail and healthcare organizations that suffered significant disruptions from ransomware attacks traced to compromised IT outsourcing partners.
Organizations did achieve some positive developments in breach response capabilities. The mean time to identify and contain breaches fell to 241 days: representing a nine-year low in response times. Companies leveraging extensive security AI and automation identified and contained breaches 80 days faster while achieving cost savings of nearly $1.9 million compared to organizations without these advanced technologies.
Cost Drivers and Hidden Expenses
Beyond direct remediation costs, organizations in 2025 faced mounting expenses from regulatory penalties, legal settlements, and business disruption. Intellectual property theft, while less common than personal data compromise, carried the steepest per-record cost at $178. Meanwhile, customer personal identifiable information was involved in 53% of all breaches, creating ongoing liability concerns for affected organizations.
The geographic distribution of costs revealed stark disparities, with US organizations paying the highest price globally at $10.22 million per breach: nearly 2.3 times the global average. This premium reflects America's complex regulatory environment, higher legal costs, and increasingly aggressive class-action litigation following data breaches.
Emerging Threat Patterns
The Human Element Remains Dominant
Despite significant investments in automated security technologies, human factors continued to dominate the breach landscape in 2025, contributing to 60% of all incidents. This encompasses both malicious insider activity, as demonstrated in the Coinbase contractor breach, and unintentional security lapses that create entry points for external attackers.
Artificial Intelligence-Powered Attacks
A concerning evolution emerged with AI-driven attacks accounting for 1 in 6 breaches during 2025. These sophisticated attacks demonstrated unprecedented efficiency in bypassing traditional security measures, adapting in real-time to defensive responses, and identifying previously unknown vulnerabilities in target systems.
Vulnerability Exploitation Surge
System vulnerability exploitation surged dramatically in 2025, with 20% of data breaches involving the exploitation of unpatched security flaws: representing a 34% increase from the previous year. This surge was partially attributed to the proliferation of zero-day exploits specifically targeting edge devices and IoT infrastructure.
Essential Protection Strategies for Your Business
Implement Zero Trust Architecture
The breach patterns of 2025 demonstrate that traditional perimeter-based security models are insufficient against modern threats. Zero Trust architecture assumes no user or device should be trusted by default, regardless of their network location. This approach requires continuous verification of all access attempts and significantly reduces the impact of both insider threats and external breaches.
Strengthen Third-Party Risk Management
Given that vendor compromises represented the second most costly breach type, organizations must extend their security perimeter to include all connected partners. This requires comprehensive vendor security assessments, contractual security requirements, and continuous monitoring of partner ecosystems throughout the relationship lifecycle.
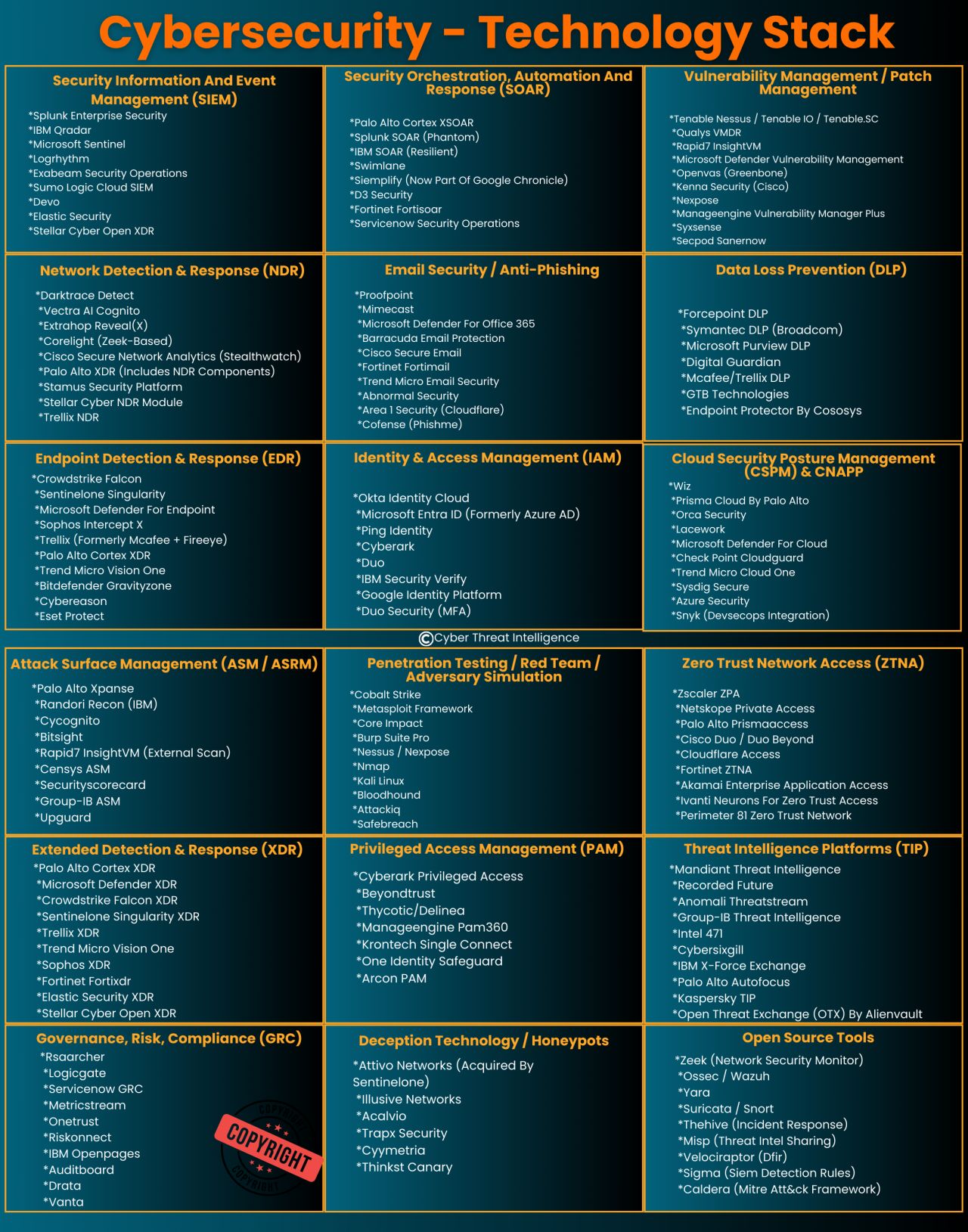
Deploy Advanced AI Security Solutions
Organizations with extensive security AI and automation demonstrated 80-day faster breach identification and achieved $1.9 million in cost savings compared to those without these technologies. Modern AI security solutions can detect anomalous behavior patterns, respond to threats automatically, and adapt to evolving attack methodologies faster than human-managed systems.
Enhance Cloud Security Posture
With 72% of breaches involving cloud-stored data, organizations must prioritize cloud security configuration management, encryption at rest and in transit, and multi-factor authentication across all cloud services. Regular cloud security assessments and automated compliance monitoring help identify and remediate vulnerabilities before they can be exploited.
Establish Comprehensive Incident Response Procedures
Reducing the average 241-day breach lifecycle requires prepared incident response capabilities. This includes regular tabletop exercises, clear communication protocols, pre-established relationships with cybersecurity experts, and documented procedures for various breach scenarios.
Your Next Steps in Cybersecurity
The data breach landscape of 2025 underscores a fundamental truth: cybersecurity is not a one-time investment but an ongoing strategic imperative. Organizations that proactively address these evolving threats through comprehensive risk management, advanced technology adoption, and continuous employee education significantly reduce both their likelihood of experiencing a breach and the potential financial impact if one occurs.
The patterns revealed by 2025's major breaches: from IoT vulnerabilities and third-party risks to AI-powered attacks and cloud misconfigurations: require specialized expertise and dedicated resources to address effectively. Many businesses find themselves overwhelmed by the complexity and constantly evolving nature of cybersecurity requirements.
At Comm Tech, MSP Inc., we understand that effective cybersecurity goes beyond deploying the latest technology: it requires a comprehensive approach that combines advanced technical solutions with practical business processes and employee education. Our breach mitigation services help organizations prepare for, respond to, and recover from security incidents while minimizing financial impact and operational disruption.
Additionally, our Cyber Security Safety Training programs equip your team with the knowledge and skills necessary to recognize and respond appropriately to evolving cyber threats. Since 60% of breaches involve human factors, investing in comprehensive employee education represents one of the most effective security measures your organization can implement.
Do not wait for a security incident to expose vulnerabilities in your organization's defenses. Contact Comm Tech, MSP Inc. today to discuss how our breach mitigation services and cybersecurity training can protect your business from becoming the next cautionary tale in cybersecurity. Your proactive investment in comprehensive security measures today can save millions in potential breach costs tomorrow.
Contact us to schedule a comprehensive security assessment and learn how we can strengthen your organization's cybersecurity posture against the evolving threats of 2025 and beyond.
