Artificial intelligence is no longer just a buzzword or a futuristic concept. It is here, reshaping how we work, communicate, and unfortunately, how cybercriminals attack. While AI brings tremendous opportunities for business efficiency and innovation, it also arms bad actors with tools that make cyberattacks faster, smarter, and far more convincing than ever before.
For Colorado small and medium-sized businesses, this shift presents a critical challenge. You are facing an enemy that learns, adapts, and strikes with precision: all while your team may still be relying on security practices designed for yesterday's threats. The question is no longer whether your business will be targeted, but whether you will be ready when it happens.
The New Face of Cyber Threats
Traditional cyberattacks required time, effort, and a certain level of technical skill. Attackers had to manually research targets, craft phishing emails one by one, and hope their malware would slip past basic security measures. AI has changed all of that.
Today's cybercriminals leverage machine learning algorithms to analyze thousands of potential vulnerabilities in seconds. They use natural language processing to generate phishing emails that are virtually indistinguishable from legitimate communication. They deploy adaptive malware that changes its behavior in real time to evade detection systems.
AI-Powered Phishing: The Perfect Impersonation
Phishing has always been one of the most effective attack vectors, but AI has supercharged its capabilities. Gone are the days of poorly written emails with obvious red flags. Modern AI-powered phishing campaigns analyze your communication patterns, mimic writing styles, and personalize messages based on publicly available information about your business and employees.
An attacker can now study your vendor relationships through social media and public records, then craft an invoice that looks exactly like what your accounting team expects to receive. The email address may be slightly altered, but everything else: tone, formatting, timing: appears authentic. One click, and your network is compromised.

Deepfakes: When Seeing Is No Longer Believing
Perhaps even more concerning is the rise of deepfake technology in business fraud. Deepfakes use AI to create convincing audio and video impersonations of real people. Imagine receiving a video call from your CEO requesting an urgent wire transfer, only to discover later that it was a sophisticated fake.
This is not science fiction. Multiple companies have already fallen victim to deepfake-enabled fraud, losing hundreds of thousands of dollars in minutes. For Colorado businesses, where relationships and trust form the foundation of commerce, this technology represents a fundamental shift in how we verify identity and authority.
The Speed Problem
AI does not just make attacks more convincing: it makes them faster. Automated reconnaissance tools can scan your network, identify weaknesses, and launch coordinated attacks before traditional security systems even register a threat. Zero-day exploits, once rare and valuable, can now be discovered and weaponized at scale.
For small and medium-sized businesses without dedicated security teams, this speed creates an impossible situation. By the time you detect an intrusion, significant damage may already be done.
Why Colorado SMBs Are Particularly Vulnerable
Colorado's business landscape, while vibrant and innovative, presents unique security challenges. Many local SMBs operate with lean IT teams or rely on part-time technical support. You may have invested in basic security measures: firewalls, antivirus software, periodic updates: but these foundational tools were not designed to combat AI-driven threats.
Additionally, Colorado businesses often operate in sectors that handle sensitive data: healthcare, legal services, financial advising, and professional services. This makes you attractive targets. Attackers know that smaller organizations often lack the resources for advanced security infrastructure while still maintaining valuable data worth stealing or holding for ransom.
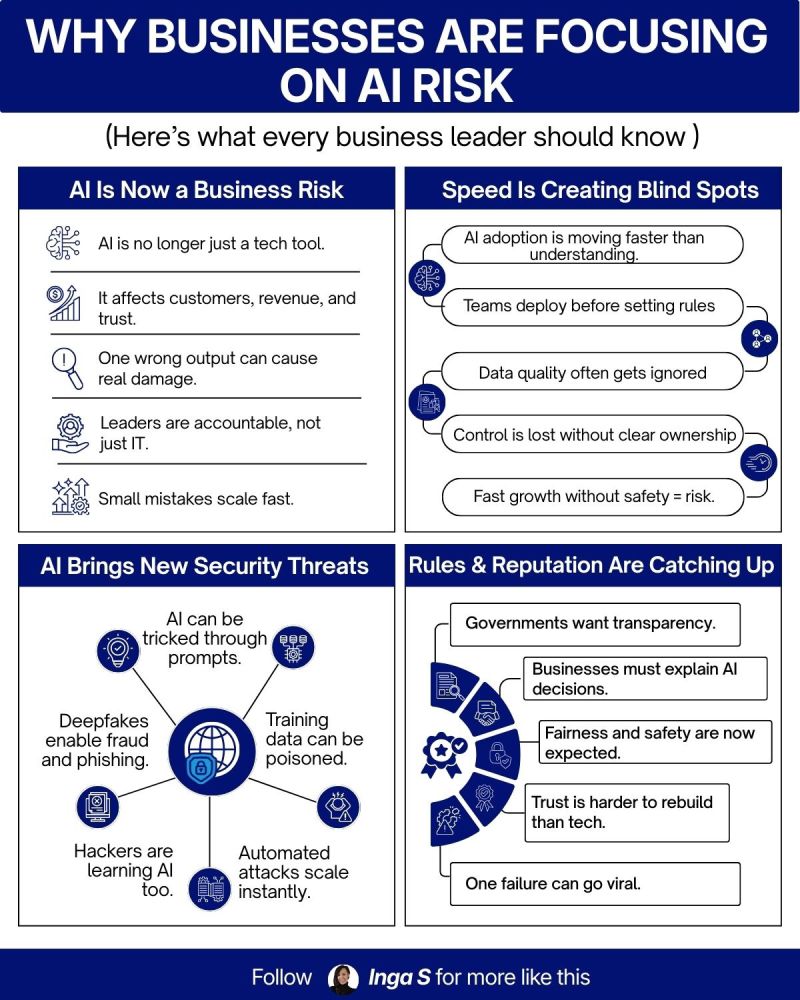
The gap between adoption speed and security governance has widened dramatically. Many organizations experiment with AI tools to improve productivity without fully understanding the security implications. Each new AI application, each connected device, each cloud service expands your attack surface, creating more potential entry points for sophisticated threats.
Building a Modern Defense Strategy
Defending against AI-powered attacks requires more than simply updating your antivirus software. You need a comprehensive, layered approach that combines advanced technology with human expertise and proactive governance.
Advanced Detection and Response
Modern security platforms use machine learning to identify anomalies and behavioral patterns across your network. These systems can detect subtle indicators of compromise that traditional signature-based tools would miss. When an employee's account suddenly starts accessing files they have never touched before, or network traffic patterns shift unexpectedly, AI-enhanced detection systems flag these activities for immediate investigation.
However, technology alone is insufficient. Automated detection must be paired with skilled security professionals who can interpret alerts, investigate incidents, and implement appropriate responses. This is where managed IT services become essential for most Colorado SMBs.
Strengthening Your Security Foundation
Advanced AI threats do not eliminate the need for strong fundamentals. In fact, many AI-powered attacks succeed because organizations have neglected basic security hygiene. Your defense strategy must include:
- Regular patching and updates across all systems and applications
- Network segmentation to limit the spread of potential breaches
- Strong identity and access management with multi-factor authentication
- Secure configuration of all devices and services
- Regular security awareness training for all employees

Zero Trust Architecture
The traditional security model assumed that threats came from outside your network. Once someone was inside, they were generally trusted. AI-driven attacks have made this approach obsolete.
Zero trust architecture assumes that no user or system is inherently trustworthy. Every access request must be verified, every connection authenticated, and every transaction monitored. This approach significantly reduces the damage an attacker can cause even if they manage to breach your perimeter defenses.
The Human Element
Your employees remain both your greatest vulnerability and your strongest defense. Security awareness training must evolve beyond once-a-year presentations. Your team needs ongoing education about emerging threats, regular simulated phishing exercises, and clear protocols for reporting suspicious activity.
When employees understand how AI-powered attacks work and know what to look for, they become active participants in your security posture rather than passive weak points.
The Role of Managed IT Services
For most Colorado SMBs, building and maintaining an in-house security team capable of defending against AI-driven threats is neither practical nor affordable. This is precisely why managed IT service providers have become critical partners in modern cybersecurity.
A qualified MSP brings enterprise-level security expertise and technology to businesses of all sizes. They monitor your systems around the clock, deploy advanced detection platforms, manage security updates, and respond to incidents with the urgency and skill they demand. More importantly, they stay current with the rapidly evolving threat landscape, ensuring your defenses adapt as quickly as the attacks themselves.
Working with an MSP also provides access to comprehensive cybersecurity strategies that would be difficult to implement independently. From vulnerability assessments and penetration testing to incident response planning and regulatory compliance support, managed services offer a complete security framework tailored to your specific business needs and risk profile.
Moving Forward with Confidence
The age of AI has fundamentally changed cybersecurity, but it has not made protection impossible. With the right combination of technology, expertise, and proactive planning, Colorado businesses can defend themselves effectively against even the most sophisticated threats.
The key is recognizing that security is not a one-time project or a static solution. It requires ongoing attention, regular updates, and a commitment to staying ahead of emerging risks. It means viewing cybersecurity not as an IT problem, but as a fundamental business priority that deserves appropriate investment and leadership attention.
Your business does not have to navigate this landscape alone. Whether you need help assessing your current security posture, implementing advanced protection measures, or building a comprehensive defense strategy, expert guidance is available.
At Comm Tech, MSP Inc., we help Colorado businesses protect themselves against modern cyber threats while maintaining the efficiency and innovation that drive growth. If you are concerned about your organization's readiness for AI-driven attacks, contact us to discuss how we can strengthen your defenses and provide the peace of mind that comes with knowing your business is truly secure.
