Remember when spotting a phishing email was as simple as looking for typos and generic greetings? Those days are gone. In 2025, artificial intelligence has fundamentally changed the cybersecurity landscape, creating phishing campaigns so sophisticated that even your most security-aware employees are falling victim. Recent data shows that 60% of recipients now succumb to AI-generated phishing emails, with some AI-enhanced spear phishing campaigns achieving clickthrough rates as high as 54%.
For Colorado business owners and managers, this represents a critical shift in how we think about cybersecurity training and protection. The old rules no longer apply, and traditional detection methods that relied on human intuition are failing against machines that can perfectly mimic legitimate communications.
The End of "Obvious" Phishing Signs
Perfect Grammar and Professional Presentation
The grammatical errors and awkward phrasing that once served as red flags have disappeared. AI language models now produce emails that are grammatically flawless and professionally formatted. These systems can mimic corporate writing styles, match industry-specific terminology, and even replicate individual communication patterns. Your employees can no longer rely on poor writing quality as a warning sign.
Hyper-Personalization That Feels Genuine
Modern AI phishing campaigns leverage vast amounts of data scraped from social media, company websites, and public databases to create deeply personalized messages. Instead of generic "Dear Customer" greetings, attackers now reference recent company events, specific projects, or individual achievements. When an employee receives an email that mentions their recent promotion or references a meeting they attended last week, the natural response is trust.
Context-Aware Timing
AI systems monitor news cycles, industry events, and seasonal patterns to time attacks perfectly. A phishing email about tax preparation arrives in March, security updates coincide with actual software releases, and "urgent" requests align with busy periods when employees are more likely to act quickly without scrutinizing details.
Why Traditional Training Falls Short
The Speed of Adaptation
While your team learns to recognize this month's phishing tactics, AI systems are already developing next month's approaches. Machine learning algorithms analyze successful attacks, identify patterns in victim behavior, and continuously refine their strategies. Traditional annual or quarterly cybersecurity training cannot keep pace with this rate of evolution.
Real-Time Response and Adjustment
Perhaps most concerning is AI's ability to adapt during an active attack. If an employee responds with skepticism or asks clarifying questions, AI-powered chatbots can adjust their approach in real-time, providing plausible explanations and building trust through continued interaction. This conversational capability makes detection significantly more challenging than static email analysis.
Volume Overwhelms Vigilance
The economics of AI-generated attacks have fundamentally changed the threat landscape. Attackers can now reduce campaign costs by 95% while achieving greater success rates than human-crafted attempts. This cost reduction has led to a 1,265% surge in AI-generated phishing attacks over the past year, with approximately 83% of all phishing emails now created by artificial intelligence.
The Deepfake Dimension
Voice and Video Impersonation
Deepfake technology has introduced an entirely new category of threats that traditional training never addressed. Attackers can now create convincing audio recordings of executives requesting wire transfers or video calls with "trusted" partners soliciting sensitive information. Deepfake impersonations have increased by 15% over the past year, with particularly sophisticated attacks targeting financial decision-makers.
Multi-Modal Attacks
The most advanced campaigns now combine multiple AI technologies: personalized emails followed by deepfake phone calls, fake video conferences with AI-generated participants, and chatbot interactions that feel genuinely human. These multi-layered approaches create multiple opportunities for deception and make it extremely difficult for even trained employees to maintain consistent skepticism.
Practical Protection Strategies for Colorado Businesses
Technical Controls Over Human Judgment
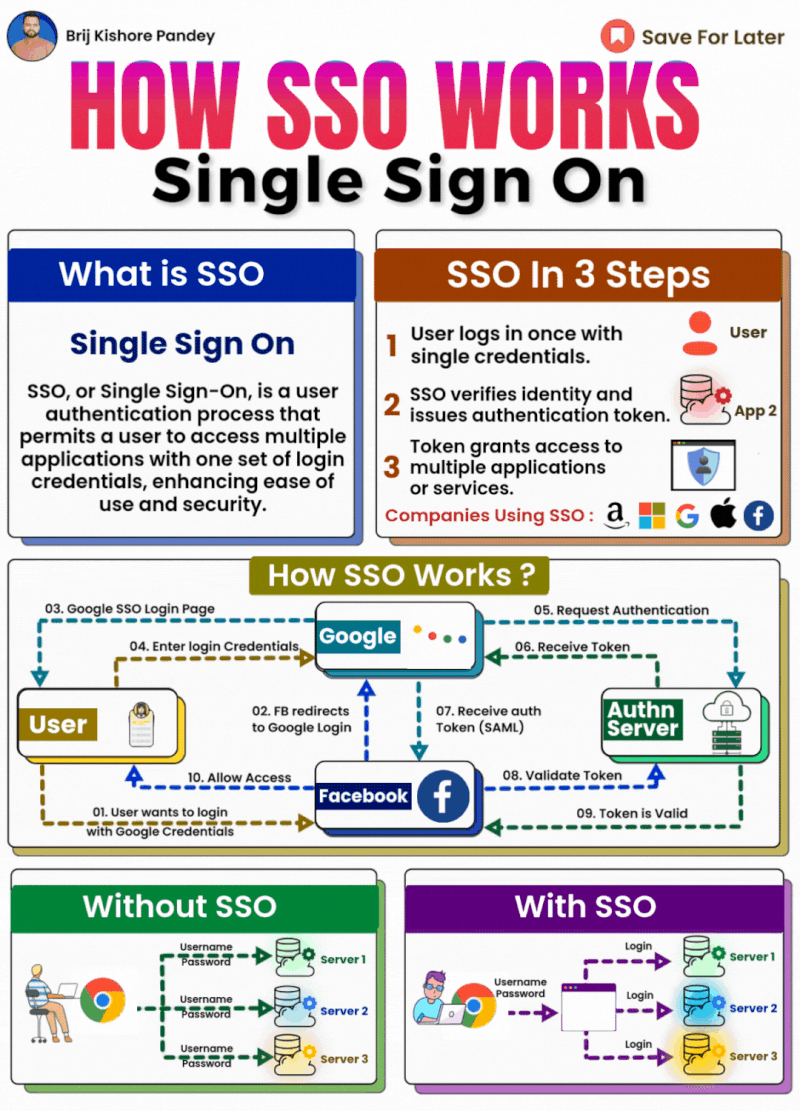
While employee training remains important, businesses must acknowledge its limitations and implement technical safeguards that do not rely on human detection. Advanced email filtering systems that analyze communication patterns, implement zero-trust verification protocols, and maintain updated threat intelligence databases provide more consistent protection than human vigilance alone.
Multi-Factor Authentication and Verification Protocols
Establish mandatory verification procedures for sensitive requests, regardless of apparent source. Financial transactions, password resets, and data access requests should require multi-factor authentication and out-of-band confirmation through separate communication channels. These protocols create barriers that AI cannot easily circumvent through social engineering.
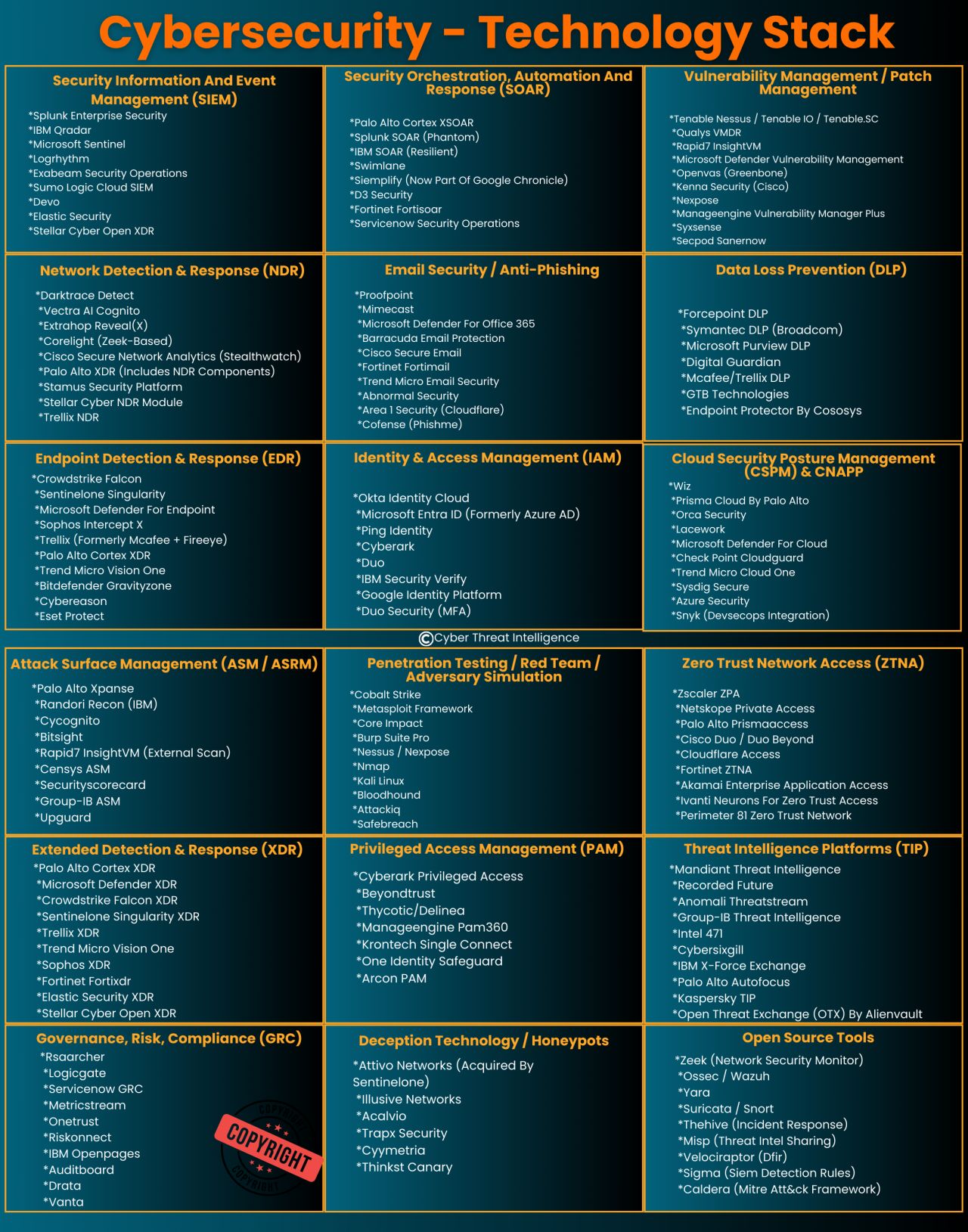
Behavioral Analytics and Anomaly Detection
Deploy systems that monitor normal communication patterns and flag unusual requests or behaviors. If an executive who typically sends brief emails suddenly sends lengthy, formal messages requesting unusual actions, automated systems can trigger additional verification steps. This approach focuses on detecting deviations from established patterns rather than relying on content analysis alone.
The Local Advantage: Why Colorado Businesses Need Specialized Support
Understanding Regional Threats
Colorado businesses face unique cybersecurity challenges, from industry-specific regulations in sectors like healthcare and finance to geographic targeting by cybercriminals who understand local business practices. Attackers increasingly tailor their campaigns to regional characteristics, making local cybersecurity expertise more valuable than ever.
Rapid Response and Personal Relationships
When an AI-powered attack succeeds, response time determines impact severity. Local managed service providers can provide immediate, hands-on assistance rather than remote troubleshooting from distant call centers. This personal relationship approach proves especially valuable when dealing with sophisticated threats that require nuanced understanding of your business operations.
As a veteran and women-owned MSP serving the Denver metro area, we understand that effective cybersecurity requires both advanced technology and personal attention to your unique business needs.
Moving Beyond Training-Only Approaches
Continuous Monitoring and Updates
Effective protection requires continuous monitoring of threat landscapes, regular updates to security protocols, and ongoing assessment of emerging attack vectors. This level of vigilance exceeds what most internal IT teams can maintain while managing daily operations.
Integrated Security Ecosystems
Modern cybersecurity requires coordinated systems: email security, endpoint protection, network monitoring, and incident response capabilities must work together seamlessly. Piecemeal solutions create gaps that AI-powered attacks can exploit.
The sophistication of AI-powered phishing campaigns represents a fundamental shift in cybersecurity threat landscapes. While employee awareness remains important, businesses cannot rely solely on human detection capabilities to protect against machine-generated attacks that continuously adapt and improve.
Colorado businesses need comprehensive, professionally managed cybersecurity strategies that combine advanced technical controls with local expertise and rapid response capabilities. The investment in robust managed IT security services pays for itself many times over when compared to the potential costs of successful attacks.
Ready to strengthen your defenses against AI-powered threats? Contact Comm Tech, MSP Inc. to discuss how our comprehensive cybersecurity solutions can protect your business from evolving digital threats while maintaining the operational efficiency your team depends on.
