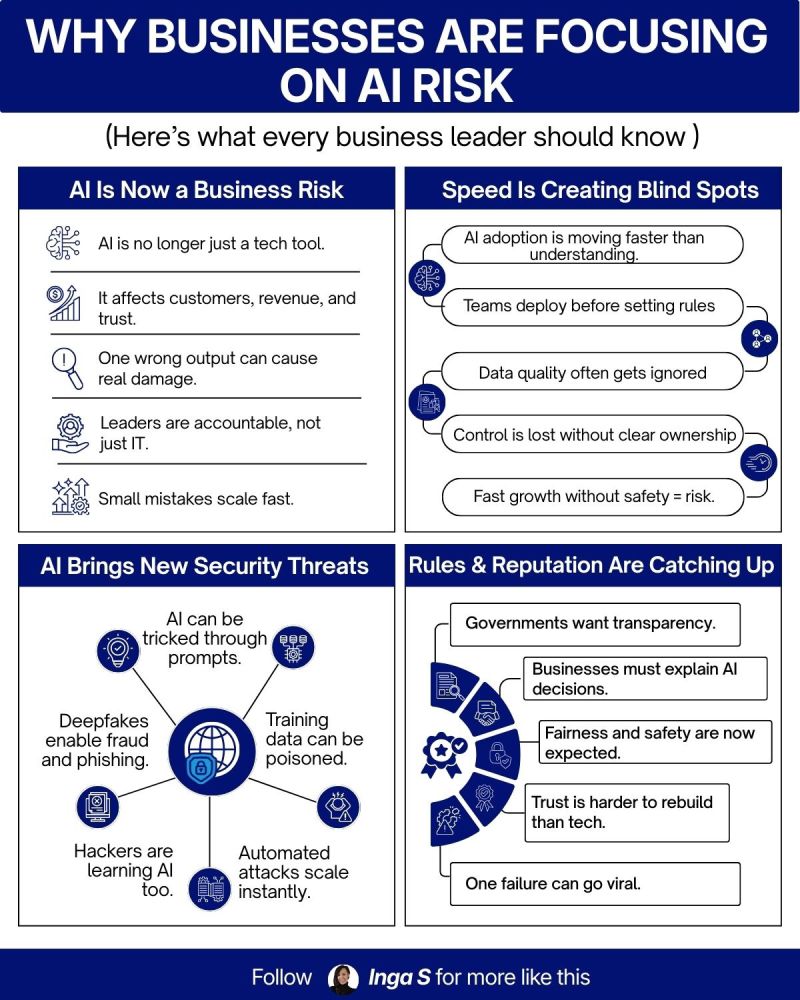
As we navigate the first quarter of 2026, the landscape of healthcare and private practice technology has shifted significantly. For years, cybersecurity was treated as a "bolt-on" feature: a digital insurance policy or a software package installed after the fact. However, the sophistication of ransomware actors has rendered this reactive approach obsolete.
For private practices today, whether in the medical, dental, or legal fields, the stakes have never been higher. Ransomware in 2026 is no longer just about encrypting files; it is about "triple extortion," where attackers encrypt data, steal sensitive patient records to leak online, and target your third-party vendors simultaneously. To combat this, successful practices are moving toward a Cyber-First Model.
A Cyber-First model means that security is the foundation of every IT decision you make. From the moment you onboard a new employee to the day you integrate a new Electronic Health Record (EHR) system, security is the lead act, not a post-script.
Why Private Practices are Primary Targets
You might wonder why a small or mid-sized private practice would be targeted over a large hospital system. The answer is simple: accessibility and value. Attackers know that private practices often have smaller IT budgets and less rigorous security protocols than multi-state hospital networks, yet they house the same high-value Protected Health Information (PHI).
In 2026, the "cost" of a ransomware attack is no longer measured solely by the ransom demand. It includes the cost of downtime, federal fines for HIPAA violations, and, perhaps most damagingly, the loss of patient trust. According to industry data, over 65% of healthcare organizations faced a ransomware attempt in the last year. For a private practice, a week of downtime can be a terminal event.
The Cyber-First Architecture
Adopting a Cyber-First model requires a shift in mindset. It begins by acknowledging that your network perimeter is no longer a physical wall around your office. In the age of telehealth and remote administrative work, your perimeter is everywhere your data lives.
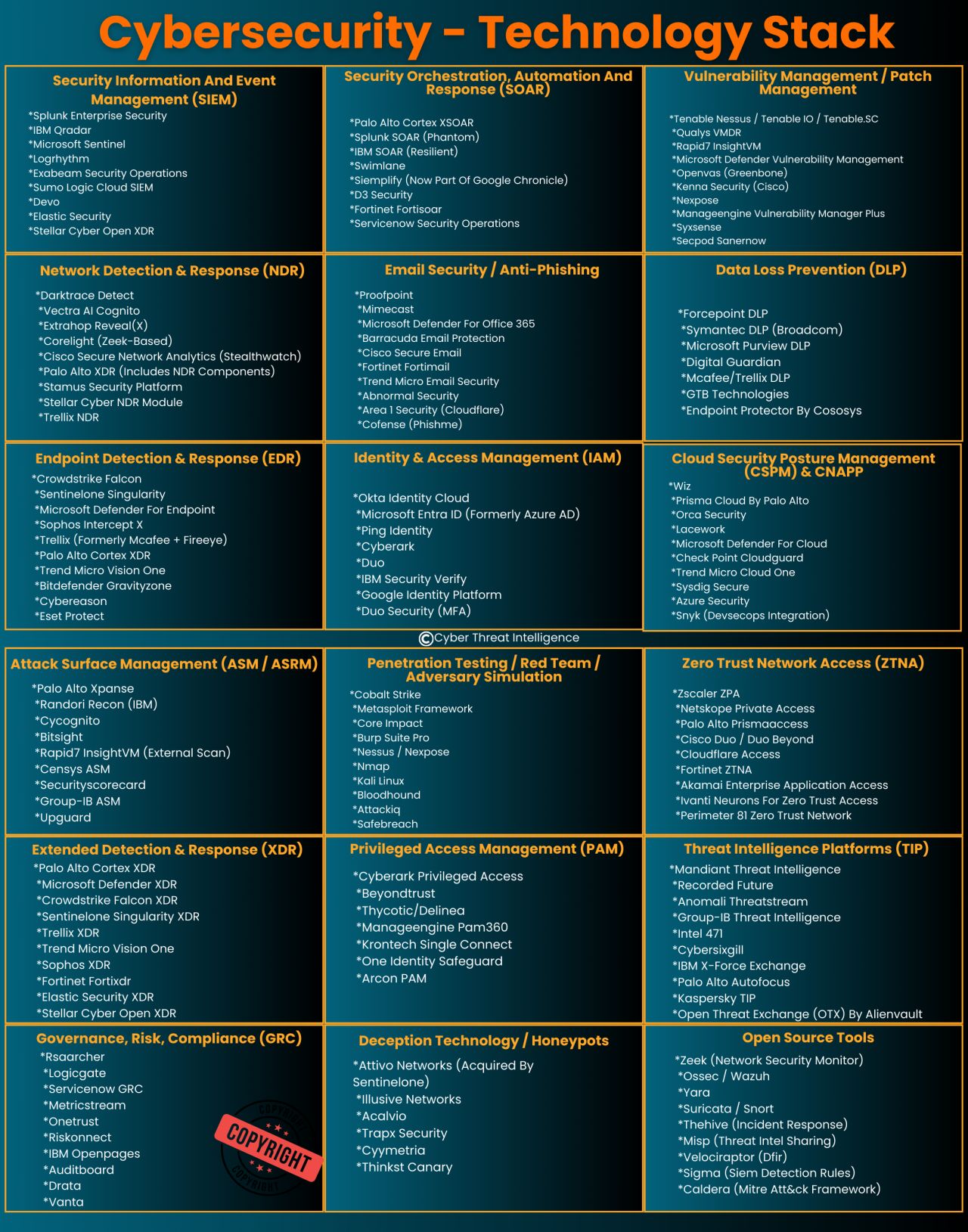
To build a foundation that can withstand 2026-era threats, your managed IT services should focus on these core pillars:
1. Identity as the New Perimeter
In a Cyber-First model, we assume the network is already compromised. Therefore, the most critical gatekeeper is the identity of the user. Most ransomware attacks today begin with compromised credentials: often through sophisticated phishing or social engineering.
Multi-Factor Authentication (MFA) is no longer optional; it is the absolute minimum requirement. However, in 2026, we advocate for "Phishing-Resistant MFA," which uses hardware keys or biometric verification rather than simple SMS codes.
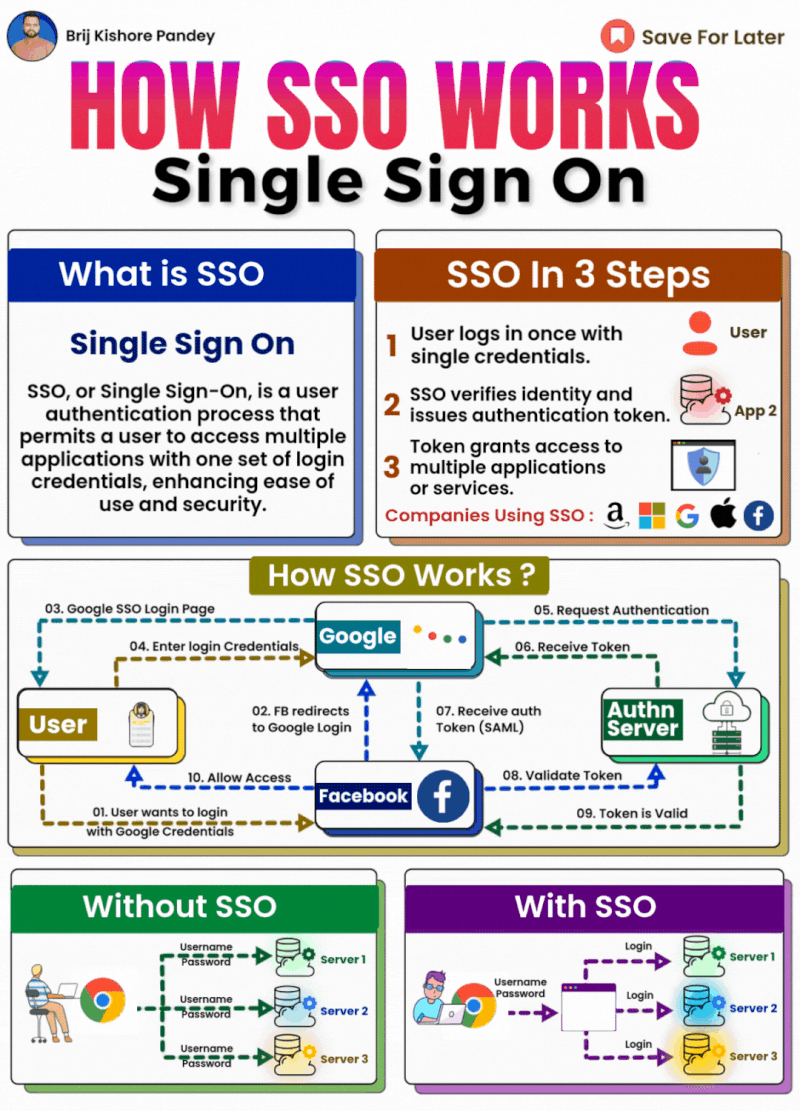
Single Sign-On (SSO) is another essential component. By centralizing where your staff logs in, you can monitor for anomalies more effectively and revoke access instantly if a threat is detected.
2. Immutable Data Protection (BCDR)
The "R" in ransomware stands for the ransom demanded to get your data back. But what if you didn't need their decryption key? This is where Business Continuity and Disaster Recovery (BCDR) becomes your practice's strongest leverage.
In 2026, traditional backups are often targeted first by ransomware to ensure the victim has no choice but to pay. A Cyber-First strategy employs Immutable Backups. These are "write-once-read-many" files that cannot be changed, deleted, or encrypted by ransomware, even if the attacker gains administrative access to your network.
By maintaining an air-gapped or immutable copy of your data, Comm Tech, MSP Inc. ensures that your practice can be restored to a clean state in hours, not weeks.
3. AI-Driven Endpoint Detection and Response (EDR)
Traditional antivirus software looks for "signatures" of known viruses. Modern ransomware, however, is polymorphic: it changes its code constantly to avoid detection.
A Cyber-First practice utilizes Endpoint Detection and Response (EDR). EDR uses artificial intelligence to monitor behavior rather than just file names. If a computer suddenly begins encrypting hundreds of files at 2:00 AM, the EDR system recognizes this as "malicious behavior," kills the process, and isolates the machine from the rest of the network automatically.

4. Network Segmentation and Zero-Trust
In many older practices, once a user logs into the front desk computer, they have a "straight line" to the server and the medical imaging devices. This is a gift to ransomware, allowing it to spread laterally across your entire office.
Network Segmentation involves breaking your network into isolated "islands." Your guest Wi-Fi should never talk to your EHR server. Your medical devices (like X-ray machines or vitals monitors) should be on their own secure segment. By implementing Zero-Trust principles, every device and user must be verified every time they attempt to access a new resource, significantly slowing down or stopping the spread of an infection.
The Human Factor: Training in the Age of AI
Even the most advanced technical stack can be undone by a single distracted click. In 2026, phishing attacks are no longer characterized by poor grammar and suspicious "Prince" stories. They are highly personalized, often using AI to mimic the writing style of your colleagues or vendors.
Security awareness training must be continuous. At Comm Tech, MSP Inc., we recommend:
- Monthly Phishing Simulations: Testing your staff with realistic, non-punitive exercises.
- Role-Specific Training: Front-desk staff face different threats than clinical providers or billing specialists.
- Incident Reporting Culture: Ensuring your team knows that reporting a "wrong click" immediately is a heroic act, not a fireable offense. Early detection is the difference between a minor reboot and a total outage.
Your 30-Day Ransomware Prevention Checklist
Transitioning to a Cyber-First model doesn't happen overnight, but you can take immediate steps to harden your practice’s defenses.
- Audit Your MFA: Ensure MFA is enabled on your email, your EHR, and your remote access portals (VPNs). If it’s not turned on, do it today.
- Verify Your Backups: Ask your IT provider when the last "full restore test" was performed. Knowing you have a backup is different from knowing that backup actually works.
- Patch Your Systems: Ensure all medical devices and workstations are updated. Ransomware often exploits "vulnerabilities" that manufacturers fixed months ago but the practice never installed.
- Review Access Levels: Follow the "Principle of Least Privilege." Does your receptionist need administrative access to the server? If not, remove it.
The Partnership Approach
The burden of cybersecurity shouldn't fall solely on the shoulders of the Practice Manager or the lead physician. Managing these layers of defense requires constant vigilance and specialized expertise that most internal teams simply don't have the time to maintain.
At Comm Tech, MSP Inc., we believe in a partnership that goes beyond fixing broken computers. We serve as your strategic technology partner, ensuring that your security posture evolves faster than the threats. By putting security at the forefront of your IT strategy, you aren't just protecting data; you are protecting your reputation and the health of your patients.
Final Thoughts
The 2026 guide to ransomware prevention is not about a single "silver bullet" software. It is about a comprehensive, Cyber-First culture. When security leads the act, technology becomes an accelerator for your practice rather than a source of anxiety.
If you are concerned that your current IT setup is treating security as an afterthought, we invite you to reach out for a consultation. Let’s build a foundation that keeps your practice safe, compliant, and ready for whatever the digital landscape holds next.
Ready to secure your practice? Contact us today to learn more about our Cyber-First managed services and how we can protect your data from the evolving threats of 2026.
